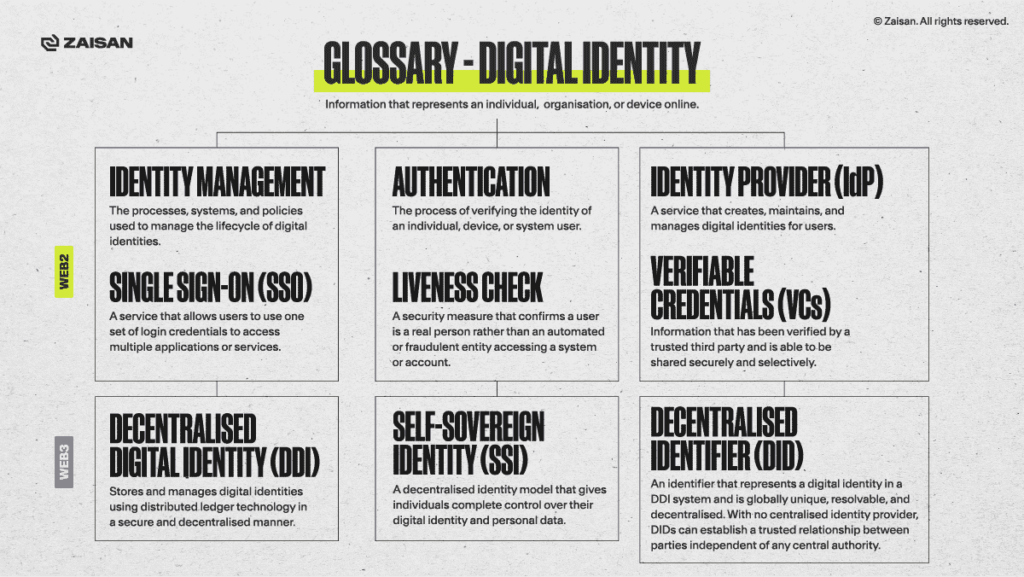
Within the digital identity ecosystem, verifiable credentials (VCs) refer to an open standard for digital credentials that represent information that would normally be found in passports, driver’s licences, university titles, and other forms of accreditation.
In this post, we explain the mechanics underpinning VCs and some potential use cases.
In another time and another place, there were trustworthy knights.
Ivanhoe is one of Walter Scott’s best-known works. Deemed a historical romance novel, the story follows Wilfred of Ivanhoe, a Saxon knight, and his beloved, Lady Rowena. The thrust of the plot is Ivanhoe’s determination to marry Lady Rowena, with whom he grew up with after Rowena was orphaned and became the ward of Wilfred’s father, Cedric, a powerful Saxon lord. The conflict arises when Cedric betroths Rowena to another, Athelstane, out of political interest.
Wilfred is portrayed as the epitome of chivalry. He’s heroic, honourable, and loyal. Rowena is equally depicted as chaste, virtuous, and loyal to her true feelings of love for Ivanhoe. Becoming a knight was a big deal in those days. Indeed, knighthood came to be considered a form of nobility, though on a lower scale. But the point is that knights were respectable, trustworthy individuals.
Knighthood could be earned by different means: prowess on the battlefield, social status or economic factors. Armour, weapons, and knight-related paraphernalia were expensive, and beyond the reach of most. But perhaps the key factor for a lord (or someone from the royalty) to bestow knighthood unto somebody was trust. A knight-to-be had to prove himself worthy of trust to the lord. This implied honour, the upholding and protection of the weak, and respect. All these attributes had to be proven before the dubbing ceremony took place, where the lord would place the flat of a sword on the shoulders of the man kneeling before him, thus bestowing knighthood upon him. A foundation of trust was vital for the lord-knight relationship to work.
The triangle of trust
Fast forward a few centuries to the present day. Blockchain technology has enabled a new identity framework, centred around digital credentials. VCs are part of that framework.
VCs stand at the centre of a triangle of trust, which features three vertices: Issuer, Holder, and Verifier. The triangle represents the following flow: the Issuer digitally signs a credential (or set of) and issues them to the Holder, which manages the credentials and, when required, presents them to the Verifier. In this context, the Issuer and the Holder trust each other. The Holder trusts the Verifier, and the Verifier trusts the Issuer. As we can see, VCs are anchored on implicit trust, much like the relationship between a knight and a lord was all those years ago. Furthermore, this identity model puts the individual (the knight, in our narrative) in control of their identity attributes.
Verifiable credentials: quick definition
We all carry a set of physical credentials in our wallets at all times. Driver licenses, government IDs, library cards, health insurance cards, a passport if we are abroad, and myriad others. These things are a) cumbersome, and b) antiquated. It is cumbersome because we have so many of them, all issued by different entities. And antiquated because, well, they come in physical form, which means they can be lost or damaged beyond usability. Both scenarios would require contacting the issuing entity’s help desk many times, and a lengthy wait until a replacement is issued.
Now imagine if, instead of having to carry all those documents on you at all times, all you had to do was show a QR code that contained all that information. If you needed to use any of your credentials, someone would just scan the QR code, and poof, voila. Done. This is the essence of VCs. A digital representation of credentials that enables the individual to selectively share their information, without having to show the actual data. VCs enable the third party to instantly verify that the information is true, without having to call or contact anyone else.
In short: VCs are tamper-proof credentials that can be instantly and cryptographically verified.
Verifiable credentials: properties and components
As specified in the W3 data model, VCs must fulfil three inherent properties. They must be:
- Machine-verifiable
- Secure and tamper-proof
- Respectful of privacy
At a technical level, VCs have three basic components: metadata, claims, and proofs
Metadata – This is information cryptographically signed by the Issuer. Metadata reflects the properties of the credential (who the issuer is, expiry date, and a public key, among many other pieces of information).
Claims – A statement about the Holder, such as the date of birth.
Proofs – Information about the Holder that accomplishes four things:
- Allows others to verify the source of the data (i.e., the issuer)
- Proves that the data belongs to the Holder, and to that Holder alone
- Guarantees that the data has not been tampered with
- Checks that the data has not been revoked by the Issuer
All this information is contained within a JavaScript Object Notation (JSON) file, an open specification format for transmitting data as a series of attributes and values, and arrays. These JSON files can then be converted into a JSON Web Token (JWT), which is essentially a JSON file with a cryptographic signature added in. These signatures are kept secure by a pair of public and private keys.
Verifiable credentials: use cases
VCs can be applied to many different aspects of identity-related frameworks. For example:
- Government-issued documents, including passports, driver’s licences, national ID cards, etc.
- Travel visas
- Healthcare certificates
- Credit scoring information
- Educational credentials (diplomas, university titles, and any other academic achievements)
- Documentation required for opening bank accounts, and applying for financial products (loans, mortgages, etc.)
- Credentials for opening a bank account or setting up payments
- Verification of disability status
This is by no means an exhaustive list. Rather, it is a sample of some of the possible solutions that VCs can be part of.
Conclusion
There are no knights in today’s world, at least not like the ones described in Ivanhoe, or so many other medieval-themed tales. But the image of the honourable and strait-laced Wilfred will do just fine for our analogy. Wilfred (and all those bestowed with a knighthood) embodied trust, truth, and honour. VCs play a very similar role, albeit several centuries later, and in a world that has moved away from the centralization of power that lords represented. You can think of VCs as the knights of a decentralised world, representing the system of trust, truth, and honour that every identity framework requires to function.
Key takeaways
- VCs stand at the centre of a triangle of trust, which features three vertices: Issuer, Holder, and Verifier
- Current standards dictate that VCs must be machine-verifiable, secure and tamper-proof, and respectful of privacy
- At a technical level, VCs have three basic components: metadata, claims, and proofs
- VC information is usually presented in JSON format, which can be converted into a JWT. This adds a cryptographic signature to the credential